#include <rsa_context.hh>
Public Member Functions | |
| rsa_context (int keylen) | |
| rsa_context (const std::string &filename, const std::string &passwd) | |
| rsa_context (const char *filename, const char *passwd) | |
| int | get_key_bits () |
| int | max_ptext_bytes () |
| bool | is_crt_available () |
| virtual void | pub_encrypt (unsigned char *out, int *out_len, const unsigned char *in, int in_len) |
| virtual void | priv_decrypt (unsigned char *out, int *out_len, const unsigned char *in, int in_len) |
| virtual void | priv_decrypt_batch (unsigned char **out, int *out_len, const unsigned char **in, const int *in_len, int n) |
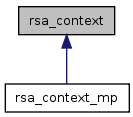
class rsa_context
Interface for RSA processing.
| rsa_context::rsa_context | ( | int | keylen | ) |
Constructor. It will randomly generate the RSA key pair with the given key length.
| keylen | Length of key in bits. Supported length are 512, 1024, 2048, and 4096 bits. |
00012 { 00013 assert(keylen == 512 || keylen == 1024 || keylen == 2048 || keylen == 4096); 00014 00015 BIGNUM *e = BN_new(); 00016 BN_set_word(e, RSA_F4 /* 65537 */); 00017 00018 rsa = RSA_new(); 00019 RSA_generate_key_ex(rsa, keylen, e, NULL); 00020 assert(RSA_check_key(rsa)); 00021 BN_free(e); 00022 00023 set_crt(); 00024 00025 bn_ctx = BN_CTX_new(); 00026 elapsed_ms_kernel = 0.0f; 00027 };

| rsa_context::rsa_context | ( | const std::string & | filename, | |
| const std::string & | passwd | |||
| ) |
Constructor. It will load key from the file using the given password. Currently supports PEM format only
| filename | file path that contains the rsa private key | |
| passwd | password used to encrypt the private key |
00030 { 00031 rsa_context(filename.c_str(), passwd.c_str()); 00032 }

| rsa_context::rsa_context | ( | const char * | filename, | |
| const char * | passwd | |||
| ) |
Constructor. It will load key from the file using the given password. Currently supports PEM format only
| filename | file path that contains the rsa private key | |
| passwd | password used to encrypt the private key |
00035 { 00036 BIO *key; 00037 OpenSSL_add_all_algorithms(); 00038 00039 key = BIO_new(BIO_s_file()); 00040 assert(key != NULL); 00041 assert(BIO_read_filename(key, filename) == 1); 00042 rsa = PEM_read_bio_RSAPrivateKey(key, NULL, NULL, (void *)passwd); 00043 ERR_print_errors_fp(stdout); 00044 BIO_free(key); 00045 00046 set_crt(); 00047 00048 bn_ctx = BN_CTX_new(); 00049 elapsed_ms_kernel = 0.0f; 00050 };
| int rsa_context::get_key_bits | ( | ) |
| bool rsa_context::is_crt_available | ( | ) |
| int rsa_context::max_ptext_bytes | ( | ) |
| void rsa_context::priv_decrypt | ( | unsigned char * | out, | |
| int * | out_len, | |||
| const unsigned char * | in, | |||
| int | in_len | |||
| ) | [virtual] |
Decrypt the data with RSA algorithm using private key. All encryption/decryption methods assume RSA_PKCS1_PADDING
| out | Buffer for output. | |
| out_len | In: allocated buffer space for output result, Out: output size. | |
| in | Buffer that stores cipher text. | |
| in_len | Length of cipher text |
Reimplemented in rsa_context_mp.
00099 { 00100 #if 0 00101 if (is_crt_available()) { 00102 // This is only for debugging purpose. 00103 // RSA_private_decrypt() is enough. 00104 BIGNUM *c = BN_bin2bn(in, in_len, NULL); 00105 assert(c != NULL); 00106 assert(BN_cmp(c, rsa->n) == -1); 00107 00108 BIGNUM *m1 = BN_new(); 00109 BIGNUM *m2 = BN_new(); 00110 BIGNUM *t = BN_new(); 00111 00112 BN_nnmod(t, c, rsa->p, bn_ctx); 00113 BN_mod_exp(m1, t, rsa->dmp1, rsa->p, bn_ctx); 00114 BN_nnmod(t, c, rsa->q, bn_ctx); 00115 BN_mod_exp(m2, t, rsa->dmq1, rsa->q, bn_ctx); 00116 00117 BN_sub(t, m1, m2); 00118 BN_mod_mul(t, t, rsa->iqmp, rsa->p, bn_ctx); 00119 BN_mul(t, t, rsa->q, bn_ctx); 00120 BN_add(t, m2, t); 00121 00122 int ret = remove_padding(out, out_len, t); 00123 assert(ret != -1); 00124 00125 BN_free(c); 00126 BN_free(m1); 00127 BN_free(m2); 00128 BN_free(t); 00129 } else { 00130 #endif 00131 int bytes_needed = get_key_bits() / 8; 00132 assert(*out_len >= bytes_needed); 00133 00134 *out_len = RSA_private_decrypt(in_len, in, out, rsa, 00135 RSA_PKCS1_PADDING); 00136 assert(*out_len != -1); 00137 #if 0 00138 } 00139 #endif 00140 }


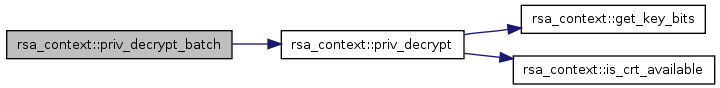
| void rsa_context::priv_decrypt_batch | ( | unsigned char ** | out, | |
| int * | out_len, | |||
| const unsigned char ** | in, | |||
| const int * | in_len, | |||
| int | n | |||
| ) | [virtual] |
Decrypt the data with RSA algorithm using private key in a batch All encryption/decryption methods assume RSA_PKCS1_PADDING
| out | Buffers for plain text. | |
| out_len | In: allocated buffer space for output results, Out: output sizes. | |
| in | Buffers that stores ciphertext. | |
| in_len | Length of cipher texts. | |
| n | Ciphertexts count. |
Reimplemented in rsa_context_mp.
00145 { 00146 assert(0 < n && n <= max_batch); 00147 00148 for (int i = 0; i < n; i++) 00149 priv_decrypt(out[i], &out_len[i], in[i], in_len[i]); 00150 }
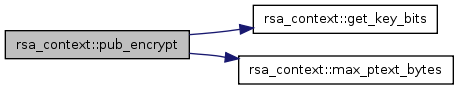
| void rsa_context::pub_encrypt | ( | unsigned char * | out, | |
| int * | out_len, | |||
| const unsigned char * | in, | |||
| int | in_len | |||
| ) | [virtual] |
Encrypts the data with RSA algorithm using public key. All encryption/decryption methods assume RSA_PKCS1_PADDING
| out | Buffer for output. | |
| out_len | In: allocated buffer space for output result, Out: out put size. | |
| in | Intput plain text. | |
| in_len | Intpu plain text size. |
00087 { 00088 int bytes_needed = get_key_bits() / 8; 00089 assert(*out_len >= bytes_needed); 00090 00091 assert(in_len <= max_ptext_bytes()); 00092 00093 *out_len = RSA_public_encrypt(in_len, in, out, rsa, RSA_PKCS1_PADDING); 00094 assert(*out_len != -1); 00095 }
 1.6.3
1.6.3